STEP 1: Remove Ads.yahoo.com pop-up ads from Internet Explorer, Firefox and Google Chrome with AdwCleaner
The AdwCleaner utility will scan your computer and web browser for the Ads.yahoo.com malicious files, browser extensions and registry keys, that may have been installed on your computer without your knowledge.- You can download AdwCleaner utility from the below link.
ADWCLEANER DOWNLOAD LINK (This link will automatically download AdwCleaner on your computer) - Before starting AdwCleaner, close all open programs and internet browsers, then double-click on the AdwCleaner icon.
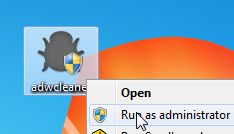
If Windows prompts you as to whether or not you wish to run AdwCleaner, please allow it to run. - When the AdwCleaner program will open, click on the Scan button as shown below.

AdwCleaner will now start to search for the Ads.yahoo.com malicious files that may be installed on your computer. - To remove the Ads.yahoo.com malicious files that were detected in the previous step, please click on the Clean button.
- AdwCleaner will now prompt you to save any open files or data as the program will need to reboot the computer. Please do so and then click on the OK
button. AdwCleaner will now delete all detected adware from your
computer. When it is done it will display an alert that explains what
PUPs (Potentially Unwanted Programs) and Adware are. Please read through
this information and then press the OK button. You will now be presented with an alert that states AdwCleaner needs to reboot your computer.
Please click on the OK button to allow AdwCleaner reboot your computer.
STEP 2: Remove Ads.yahoo.com adware with Junkware Removal Tool
Junkware Removal Tool is a powerful utility, which will remove Ads.yahoo.com pop-up ads from Internet Explorer, Firefox or Google Chrome.- You can download the Junkware Removal Tool utility from the below link:
JUNKWARE REMOVAL TOOL DOWNLOAD LINK (This link will automatically download the Junkware Removal Tool utility on your computer) - Once Junkware Removal Tool has finished downloading, please double-click on the JRT.exe icon as seen below.
![Double-click on the Junkware Removal Tool utility [Image: Junkware Removal Tool]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-icon.jpg)
If Windows prompts you as to whether or not you wish to run Junkware Removal Tool, please allow it to run. - Junkware Removal Tool will now start, and at the Command Prompt, you’ll need to press any key to perform a scan for the Ads.yahoo.com hijacker.
![Junkware Removal Tool scanning for Ads.yahoo.com pop-up virus [Image: Junkware Removal Tool scanning for Ads.yahoo.com virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/junkware-removal-tool.jpg)
Please be patient as this can take a while to complete (up to 10 minutes) depending on your system’s specifications. - When the scan Junkware Removal Tool will be completed, this utility
will display a log with the malicious files and registry keys that were
removed from your computer.
![Junkware Removal Tool final log [Image: Junkware Removal Tool final log]](http://malwaretips.com/blogs/wp-content/uploads/2013/06/Junkware-log.jpg)
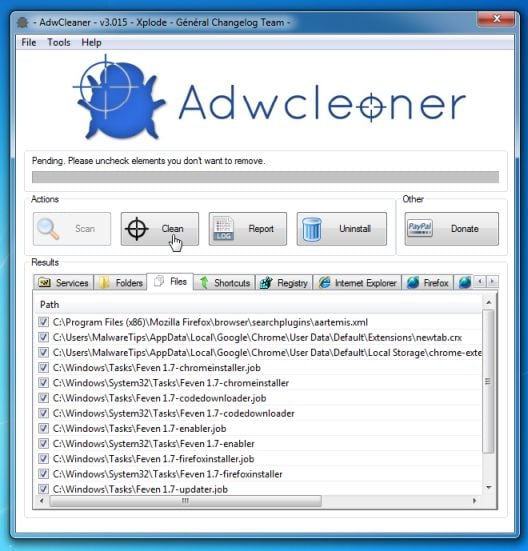
STEP 3: Remove Ads.yahoo.com pop-up virus with Malwarebytes Anti-Malware Free
Malwarebytes Anti-Malware Free uses industry-leading technology to detect and remove all traces of malware, including worms, Trojans, rootkits, rogues, dialers, spyware, and more.It is important to note that Malwarebytes Anti-Malware works well and should run alongside antivirus software without conflicts.
- You can download Malwarebytes Anti-Malware Free from the below link, then double click on it to install this program.
MALWAREBYTES ANTI-MALWARE DOWNLOAD LINK (This link will open a download page in a new window from where you can download Malwarebytes Anti-Malware Free) - When the installation begins, keep following the prompts in order to continue with the setup process.
![Malwarebytes Anti-Malware final installation screen [Image: Malwarebytes Anti-Malware final installation screen]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-installation.jpg)
- On the Scanner tab,select Perform quick scan and then click on the Scan button to start scanning your computer.
![Run a Quick Scan with Malwarebytes Anti-Malware [Image: Malwarebytes Anti-Malware Quick Scan]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-quick-scan.jpg)
- Malwarebytes’ Anti-Malware will now start scanning your computer for Ads.yahoo.com malicious files as shown below.
- When the Malwarebytes scan will be completed,click on Show Result.
![Malwarebytes when the system scan has completed [Image: Malwarebytes Anti-Malware scan results]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-scan-results.jpg)
- You will now be presented with a screen showing you the malware
infections that Malwarebytes’ Anti-Malware has detected.Please note that
the infections found may be different than what is shown in the
image.Make sure that everything is Checked (ticked) and click on the Remove Selected button.
![Click on Remove Selected to get rid of Ads.yahoo.com popups [Image:Malwarebytes removing virus]](http://malwaretips.com/blogs/wp-content/uploads/2013/01/malwarebytes-virus-removal.jpg)
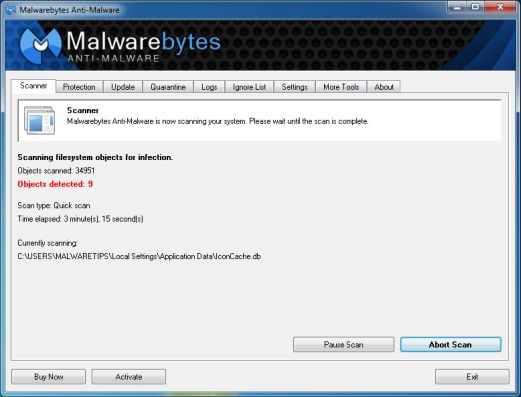
STEP 4: Double-check for the Ads.yahoo.com infection with HitmanPro
HitmanPro is a second opinion scanner, designed to rescue your computer from malware (viruses, trojans, rootkits, etc.) that have infected your computer despite all the security measures you have taken (such as anti virus software, firewalls, etc.). HitmanPro is designed to work alongside existing security programs without any conflicts. It scans the computer quickly (less than 5 minutes) and does not slow down the computer.- You can download HitmanPro from the below link, then double-click on it to start this program.
HITMANPRO DOWNLOAD LINK (This link will open a new web page from where you can download HitmanPro) - HitmanPro will start and you’ll need to follow the prompts (by clicking on the Next button) to start a system scan with this program.


- HitmanPro will start scanning your computer for Ads.yahoo.com malicious files as seen in the image below.

- Once the scan is complete,you’ll see a screen which will display all
the infected files that this utility has detected, and you’ll need to
click on Next to remove this malicious files.

- Click Activate free license to start the free 30 days trial and remove all the malicious files from your computer.
(OPTIONAL) STEP 5 : Remove the browser extension responsible for the Ads.yahoo.com pop-up ads from Internet Explorer, Firefox and Google Chrome
If you are still experiencing issues with the Ads.yahoo.com pop-up ads in Internet Explorer, Firefox or Chrome, we will need to reset your browser to its default settings. This step needs to be performed only if your issues have not been solved by the previous steps.Remove Ads.yahoo.com pop-up ads from Internet Explorer
- Open Internet Explorer, click on the gear icon
![[Image: icongear.jpg]](http://malwaretips.com/images/removalguide/icongear.jpg) (Tools for Windows XP users) at the top (far right), then click again on Internet Options.
(Tools for Windows XP users) at the top (far right), then click again on Internet Options.

- In the Internet Options dialog box, click on the Advanced tab, then click on the Reset button.
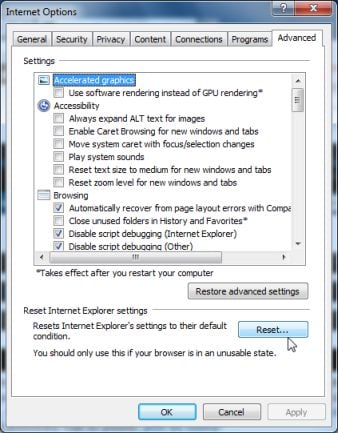
- In the Reset Internet Explorer settings section, check the Delete personal settings box, then click on Reset.
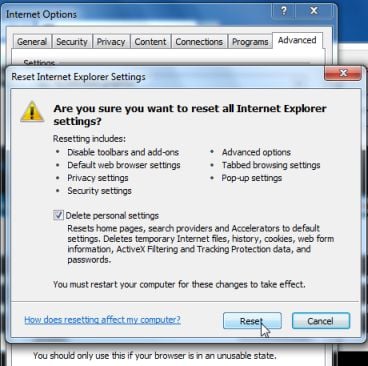
- When Internet Explorer finishes resetting, click Close in the confirmation dialogue box and then click OK.
- Close and open Internet Explorer.
Remove Ads.yahoo.com pop-up ads from Mozilla Firefox
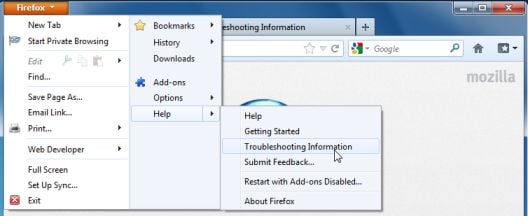
- At the top of the Firefox window, click the Firefox button, go over to the Help sub-menu (on Windows XP, click the Help menu at the top of the Firefox window), and select Troubleshooting Information.
- Click the Reset Firefox button in the upper-right corner of the Troubleshooting Information page.
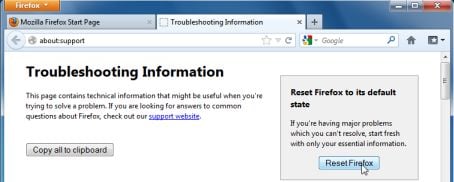
- To continue, click Reset Firefox in the confirmation window that opens.
- Firefox will close and be reset. When it’s done, a window will list the information that was imported. Click Finish
Remove Ads.yahoo.com pop-up ads from Google Chrome
- Remove Ads.yahoo.com extensions from Google Chrome.
Click the Chrome menu button on the browser toolbar, select Tools and then click on Extensions.
button on the browser toolbar, select Tools and then click on Extensions.
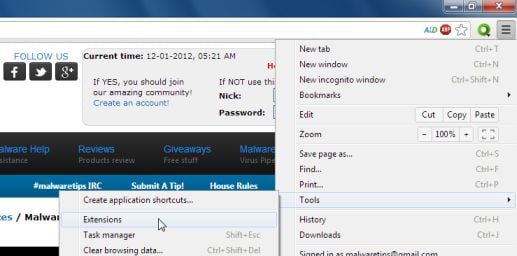
- In the Extensions tab, remove the DP1815, LyricsSay-1, LyricXeeker, Plus-HD 1.3, BetterSurf, LyricsGet, PassShow, LyricsBuddy-1, AlLyrics, ElectroLyrics-1, a2zLyrics-1, Feven 1.8, Websteroids, ScorpionSaver, HD-Plus 3.5 any other unknown extensions, by clicking the trash can
![Remove an extension from Chrome [Image: Remove an extension from Chrome]](http://malwaretips.com/blogs/wp-content/uploads/2013/07/Trash-Can-Chrome.png) icon.
icon.
Cyber criminals often change the name of malicious extension that is causing the Ads.yahoo.com pop-up ads, so if you have not installed an extensions then you should remove it from your web browser.




 Important
Important  Caution
Caution 