Quick Assist is widely used to offer remote assistance to a remote computer. If you have ever encountered Quick Assist black screen admin when trying to run a program as an administrator, keep reading to realize two methods to go into Quick Assist administrator mode.
Method 1. Disable PromptOnSecureDesktop using Registry
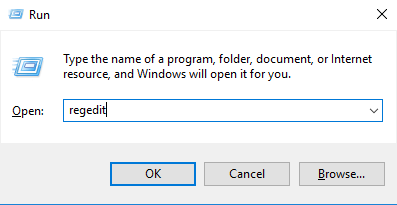
Step 1. Press Win + R to invoke the Run dialog box, then type in “regedit” and press OK to open Registry.
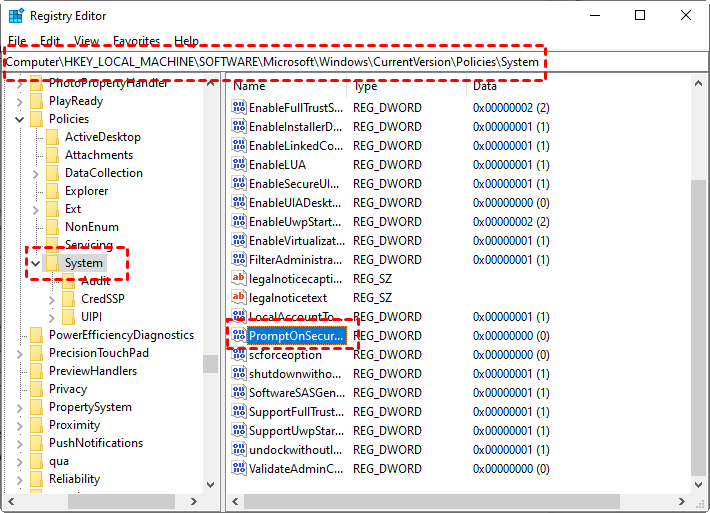
Step 2. Navigate to: Computer > HKEY_LOCAL_MACHINE > SOFTWARE > Microsoft > Windows > CurrentVersion > Policies > System. On the right pane, find and double-click PromptOnSecureDesktop.
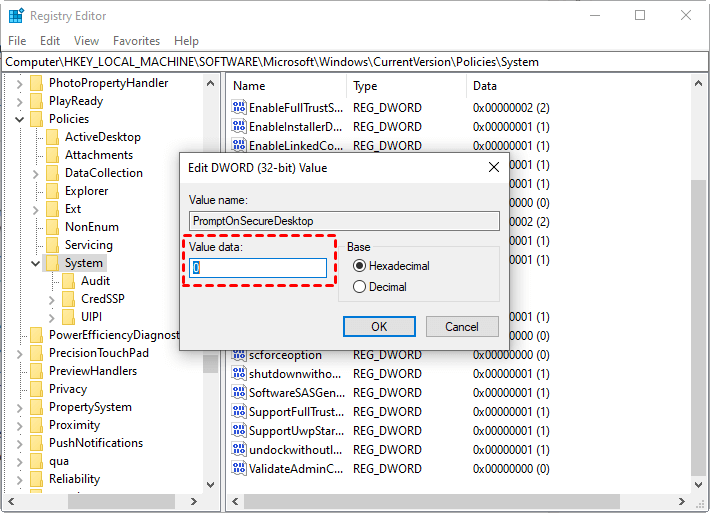
Step 3. Change its value data to 0 to disable it.
Method 2. Disable User Account Control in Group Policy
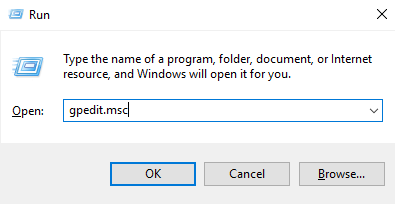
Step 1. Press Win + R to open the run dialog box, and type in “gpedit.msc” to open the Local Group Policy Editor.
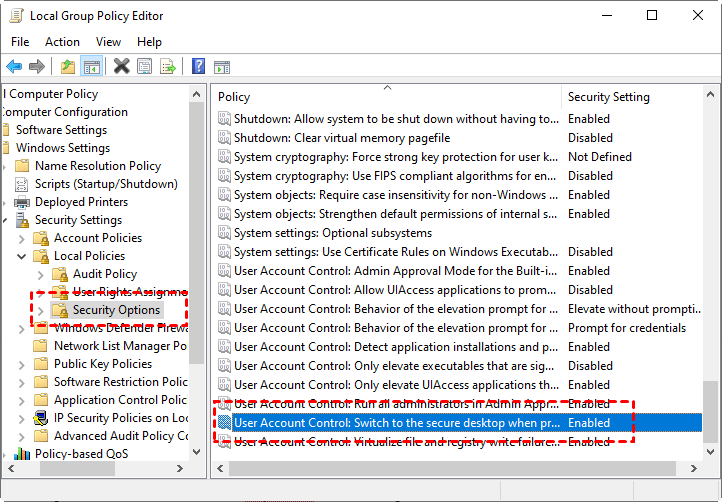
Step 2. Navigate to: Computer Configuration > Windows Settings > Security Settings > Local Policies > Security Options. Find and double-click User Account Control: Switch to the secure desktop when prompting for elevation.
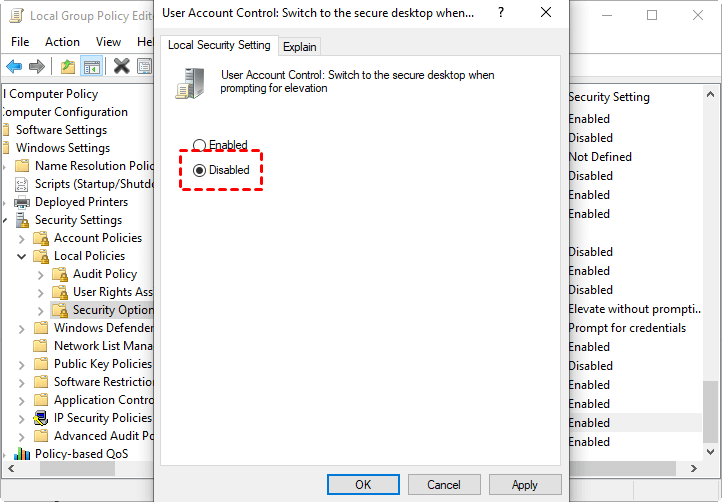
Step 3. Change its status to Disabled.
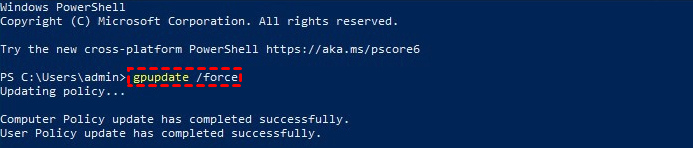
Step 4. Open Windows PowerShell and run gpupdate /force to update your computer to the latest group policy settings.
Suppose you are using Quick Assist to provide others with remote support and can’t run programs as an administrator on their computers. In that case, we provide you with two methods to help you go into Microsoft Quick Assist administrator mode. But pay attention; disabling these two policies would also be a big security risk. So please do it after careful consideration.

 These settings can be accessed through Chrome’s “Advanced Settings” menu or by navigating to “chrome://settings/."
These settings can be accessed through Chrome’s “Advanced Settings” menu or by navigating to “chrome://settings/." These settings can be accessed through the “Options” menu.
These settings can be accessed through the “Options” menu. These settings can be accessed through the “Internet Options” menu.
These settings can be accessed through the “Internet Options” menu.